According to data maintained by Johns Hopkins University, coronavirus has resulted in more than 4oo deaths and more than 20000 confirmed cases. This virus on January 31 was declared a global health emergency by WHO. With this virus on the verge of rising all over the world. Attackers on the internet have started spreading their computer virus in the name of coronavirus. Today in this blog we’re going to discuss coronavirus malware, how it started and ways to prevent it.
What Is Coronavirus Malware?
With coronavirus infecting and its fear capturing people all over the world. Cybercriminals have taken this as an opportunity to spread their malicious activities around the globe.
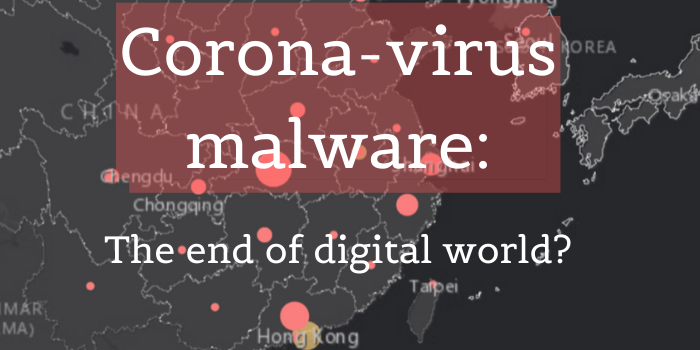
People have started receiving emails with files names “coronavirus.exe” and “novel coronavirus pneumonia.exe. Also, these files are also spreading through social media platforms WeChat.
So what’s the problem?
You might be thinking what’s the problem in receiving such emails, these files may contain some information or solution to coronavirus.
Now that’s where a majority of people get trapped. Assuming it as information or solution to coronavirus, when a user clicks to open these files, the virus gets activated and infects the device.
How does it work?
As these files are clicked by a user, their devices get infected by a trojan called “Emotet”.
These files are capable enough to destroy, steal and modify user’s data as well as infect connected computers also. All these files can disrupt the whole network of a company whose systems are connected to each other.
What Is Emotet?
This was first surfaced in 2014 and was primarily banking malware.
It was aimed to sneak onto computers to steal sensitive and private information. This trojan was developed further and got packed with spamming and malware delivery services overtime.
For instance, in earlier times this malware arrived as a javascript file.
As developments were made macro-enabled documents were being employed to get the virus payload from C&C servers run by the attackers.
This malware has the ability to surpass the detection and analysis of many antivirus software.
It senses if it’s in a virtual machine or not. It plays dead if a sandbox environment (a tool to study malware in a safe space) is detected.
Command and control servers are used by this malware to receive updates.
This can happen without any obstruction and without any signal being sent outwards.
This makes it possible for hackers to install updated malware, computer viruses in a device. Thus, making the device a safe place for all the stolen data.
Whom Does This Malware Target?
This malware can target anyone be it an individual, a company or a government agency.
An Emotet attack took place in the City of Allentown, PA. In this Microsoft’s, response team was called to rescue. It cost the city around $1m to get rid of this computer virus.
Primarily it targeted customers in Germany later on the developed version targeted organizations in Canada, UK, and the US.
How Did Coronavirus Malware Come Into The Picture?
Various cybersecurity companies constantly work towards discovering new computer viruses and malware. And Coronavirus is a result of this process.
Coronavirus malware was first discovered by IBM X-Force Threat Intelligence. And Japanese people in thickly populated areas such as Osaka, Gifu, and Tottori were its main targets.
Emails posing as official notifications from public health centres, offering solutions to coronavirus are being sent. Fearstuck people clicked and activated the virus and this is how it came into the picture.
Also, security experts at Kaspersky identified this malware spreading in form of pdf, mp4 and Docx files. These types of files come with the title- “video instructions on how to protect yourself from the virus”, “updates on the threat” and “virus detection procedures”.
According to malware analyst Anton Ivanov. Till now the cybersecurity team has discovered ten unique files that are infected. And these number will only increase as this technique gets common
Precautions To Take For This Computer Virus:-
As coronavirus will spread this type of activity will increase in other languages and countries too.
Here are some measures to protect your device from this cyberattack.
- Stay alert– study ways to spot mail spam. Don’t click or download anything thing from untrusted links. Always use google search to study any trending or relevant topic. Avoid this type of link will avoid emotet from entering your device.
- Install only authentic and official updates– Don’t get trapped into the circle of freebies, these are tactics to make the user download the malware.
- Avoid easy passwords– Keeping strong passwords that are not easy to guess are always preferred also in addition to this two-factor authentication can also be used.
- Antivirus software– Make sure to regularly run an antivirus scan on your device to avoid any virus from infecting your device.
- Keep your computers updated– Often you might ignore those updates from Microsoft, but most of the time these updates contain patches to the vulnerabilities of the previous versions so make sure to download the latest updates for your pc.
- Using tools– there are tools that offer you multilayered protection from malware you can use tools such as KASPERSKY, NORTON and Other security suites that block them in real-time.